VPNs are some really cool tools that help people protect their online privacy and anonymity. Truth be told, while that’s common knowledge by now, there are still many people who don’t have a single clue how does a VPN work. While some top-tier VPN providers do have short explanations on how their tools work, that's often not enough for the average user.
In this tutorial, we’re going to explore just that, though.
Whether you own a VPN and are just curious about the processes that are happening in the background, or this is your first time hearing the term and you have no idea how you ended up on this article, in the first place - worry not. We’ll keep things simple and avoid the technicalities - you don’t need to have a computer science degree to understand VPNs.
That said, before figuring out how does VPN work, we should probably briefly explore its main functions, right?
What is important to consider when choosing a VPN service?
One of the most important things to consider when choosing a VPN service is to make sure it has a kill switch. A kill switch kills your internet connection when the VPN service stops, which prevents any data not encrypted by the VPN from being exposed. A VPN service should also be able to work on multiple devices like your computer, TV, and mobile phone. As an extra, it should also be able to work on different operating systems, like Windows and MAC. Having a global network of servers is another plus as it can allow you access to all parts of the internet blocked off by a user's location.
Table of Contents
The Main Functions of a VPN
Right, so - the main functions of a VPN.
The most obvious use for a VPN is the preservation of online security and anonymity. The fact that you can hide your IP address (or substitute it) is a true saving grace with VPNs. After all, those are the main things that are advertised with almost every single VPN provider out there.
Note that you can always check whether your VPN is working properly or not by checking your IP address before and after turning it on. You can do so here.
People who are curious about how does a VPN work should keep that in mind. The majority of a VPN’s functionality revolves around keeping you - the user - safe while you’re browsing online and performing your own, personal activities. While I’m going to keep my promise and avoid any difficult technicalities in this “how does a VPN work?” tutorial, that’s still something worth knowing.

However, security and anonymity aside, VPNs do have some other uses, too.
One of the more well-known of these uses would have to be content streaming. This relates to any content, but the most popular examples would have to include Netflix, Hulu and HBO. You see, these companies tend to have a whole lot of region-restricted content - this means that if you live in another region than where the content airs, you ain’t gonna see it.
Unless, of course, you have a VPN at your disposal.
Because of how they work (don’t worry - this being the “how a VPN works” article, we’ll get to that), VPNs are able to trick the systems of these major content streaming platforms and grant you the access to the above-mentioned content.
Torrenting is yet another popular use for a VPN. While you’re downloading a torrented file, there’s always the chance that you might encounter a virus or a keylogger. Without having a proper VPN at your disposal, this could cause you a whole lot of issues.
With knowing how a VPN works and using one of the top VPNs in the industry, you can rest assured that no harm is going to come to your own, personal identity and other sensitive information.
So - those are some of the main functions that are attributed to most VPNs out there. Now that we’ve gotten that out of the way, let’s jump straight into the intricacies of how a VPN works.
How Does a VPN Work - The Basics
Now, in order to make this “How Does a VPN Work?” tutorial as easy to understand as possible, let’s segment it into a few different chapters. And before we move on to some of the specifics, a general, basic overview is in order.
So - how does a VPN work? VPN abbreviates as a “Virtual Private Network”. As the name implies, it is a network that’s designed with the idea of privacy in mind - hence the whole “security and anonymity” thing.
An Example for Setting the Scene
To make this part more simple, let’s use an example.
Imagine that you went to your local library to read about how does a VPN work. There, you logged on to a public WiFi connection, and remembered that you wanted to check your bank account some time ago.
As you log into your bank account, there’s a hacker on the other side of the room intercepting your connection on their own laptop. You don’t notice any disturbances per se, but the hacker managed to get the IP address of your device from your WiFi connection.
In doing so, that person now has access to your bank details, personal information, perhaps even your home address and social security number.
Now, I might have exaggerated some of that for the sake of setting a scene, but the general idea still stands.
If you were to use a VPN in that situation, you would have avoided all of that trouble you’ve just gotten yourself into. How? Well, that’s the next part of figuring out how does a VPN work.
What Happens When You Turn On a VPN?
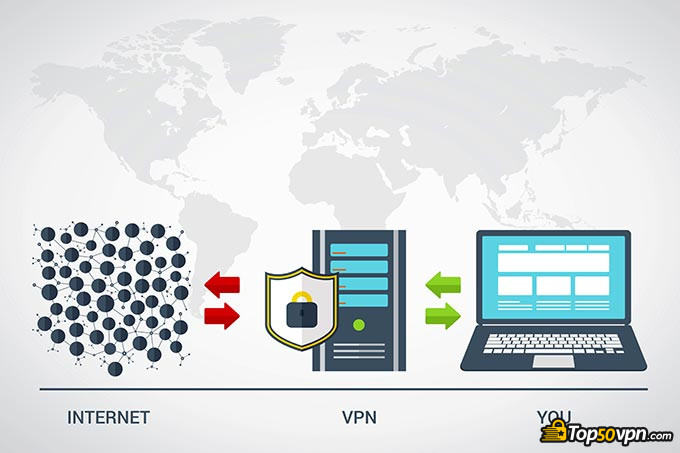
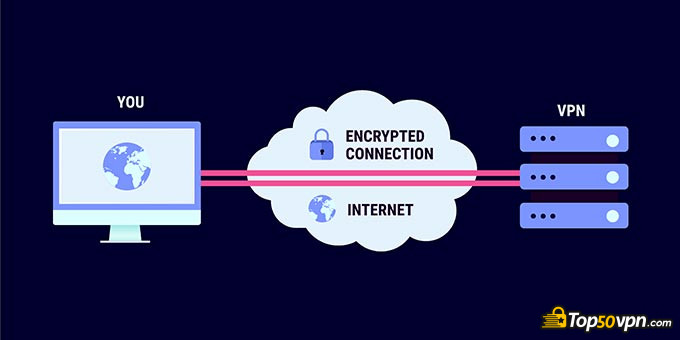
As you download, install and turn on your VPN for the very first time, a connection is then made between your device and the VPN server. You see, whenever you’re accessing a website online, you’re providing it with your credentials - IP address, location, and so on. When someone intercepts that connection, they can see all of that data.
A running VPN acts as a medium between you and the website that you’re trying to access. Your data reaches the servers of the VPN, and is then encrypted before being sent out to the site that you were trying to access.
In layman’s terms, this means that you receive a new, most commonly shared IP address. Both the website that you’re accessing and a potential hacker sees your new, fake IP - this way, your original IP is left untouched and safe.
While this can, admittedly, get a bit confusing for anyone who’s trying to learn how VPN works, just imagine that you’re sending a letter to a friend, but you don’t want them to know your address. What do you do? Well, you hire a company that forwards your letter. You send it to them, and then they send it to your friend under a fake return address.
Neither your friend, nor anyone who tries to steal your letter before it reaches its destination isn’t going to see your real address. That’s exactly how VPN works. Also, that’s why VPNs are able to provide you with the possibility of watching geo-locked content or accessing region-restricted websites.
A Closer Look - AES 256, Kill Switches and More
Now, those were some of the very basics of how VPN works. Let’s move in a bit closer and take a brief look at the processes happening in the background.
First of all, all of the major VPN providers utilize what is known as the combination of AES 256-bit data encryption and the OpenVPN protocol.
OpenVPN is a protocol that helps VPN providers implement secure and stable peer-to-peer and peer-to-site connections within their networks. It’s an industry-standard protocol, and is used by all of the major players around.
Now, AES 256 is a bit more tricky than that. As the name implies, it is a data encryption system - AES is used to encrypt the data that you send and receive, and is considered to be the strongest encryption system to date (the 256 version, that is).
That said, let me give you a pro tip out of my own, personal experience.
Whenever you learn how does a VPN work and go ahead and install a VPN of your own, always double-check whether it has AES 256 enabled by default. Most VPNs will, but there are some certain providers that have a lower version of the encryption system - AES 128 - toggled by default.
The reason for that is pretty simple - AES 256 requires a lot of resources on your end of things. This means that your connection is going to be relatively slow. That shouldn’t be your primary concern, though, since there’s nothing more important than having a secure connection.
Latest NordVPN Coupon Found:
GET 63% OFF
+ 3 Months Free
Looking for ways to secure yourself online? What if we told you that you can get the top VPN on the market for way less - grab NordVPN 60% discount now & get 3 months FREE!
Kill Switches
Kill switches are other important tools that can be found in almost every VPN that’s currently at the top of the industry.
The functionality aspect of this feature is pretty simple - whenever you’re browsing online, and experience a sudden loss of connection with your VPN, a kill switch terminates all of your processes or, in other words, shuts down all of your browser windows and terminates your downloads.
Some of the readers of this “How Does a VPN Work?” tutorial are going to say - isn’t that extremely inconvenient? And to that I reply - yes, it definitely is. But you know what else is inconvenient? Getting all of your data and sensitive personal information exposed to third parties.
A Word About VPNs and Data Logging
Now, that covers all of the main information regarding the question of how does VPN work. At this point, you should have a pretty good understanding of the basic processes that take place in the background whenever you activate your VPN.
That being said, there’s still something we should touch upon before finishing up with this “How Does a VPN Work?” tutorial - data logging.
You may or may not have heard, but data logging is one of the main issues of the VPN industry. It is a process when a VPN provider tracks your activity online and keeps logs on it, only to then sell it off to third party advertising firms or even governmental agencies.
Not cool.

Actually, it’s completely insane - that’s why there are many “exposed” articles online that talk about such providers and their shady practices.
Why am I mentioning this now? Frankly, to warn you.
Data logging isn’t going to be a major issue if you choose to use the services of one of the major VPN providers out there. However, when you start looking at some less-known names, things might also start getting shadier.
What you need to do is always read the fine print of the provider’s terms of service. Seeing as data logging is a popular topic among critics and various customer and user reviews, almost all of the better-known VPN companies now have special sections in their policies dedicated to data logging.
In these sections, you’ll find answers to all of your questions regarding data logging - does the company do it? If so, how much and what kind of your data is being logged? Is the provider going to provide that data to third parties, especially governmental agencies?

Do note, though, that not all data logging is strictly bad or out of the norm. While there are some VPN providers that log ABSOLUTELY NOTHING (read: AirVPN), the vast majority does track some certain minor information, such as billing and payment data, technical parameters, log in time (date, not hour), and so on.
All of the above-mentioned logs are kept in order to guarantee a positive experience for you, the customer. However, anything that crosses the line of customer satisfaction and intrudes on your private browsing information should be taken very seriously.
Conclusions
No matter what your reasons are for wanting to learn how does a VPN work, that’s always something that’s beneficial to know. This “How Does a VPN Work?” article should serve a basic introduction - a look behind the scenes, if you will. Naturally, things are way more complicated the deeper you venture into the topic.
However, with this article, I wanted to avoid any and all difficult technical information and some industry-specific quirks, and focus on telling you - the reader - how does VPN work in as simple of a way as possible. I hope that I’ve managed to achieve this goal, and that you are now much knowledgeable on the topic than you were some 10 minutes ago.
If you're interested in finding out more about cybersecurity and possible threats on the network, you can check out this in-depth guide.
Also, do remember to always check whether a VPN provider has a kill switch, the latest data encryption and security protocols and what is their stance on data logging, in general. If you want to be 100% sure, though, and save some time without having to need to scour the web for bits of information, you can always take a look at our list of the best VPNs of the year.
| EXPRESSVPN | CYBERGHOST | PRIVATE INTERNET ACCESS | |
| All-round security | Speed & convenience | Budget-friendly | |
| All ExpressVPN Coupons | All CyberGhost Coupons | All Private Internet Access Coupons | |
| One of the fastest VPNs in the industry. Trustworthy and safe. | Secure and Fast VPN with Great UX | Safe and reliable. Good pricing. | |
| Visit site Read review | Visit site Read review | Visit site Read review |
|---|
Table: Some of the best VPNs in the current industry
With that, I hope you’ve enjoyed the tutorial, and if you did, be sure to check out our other works. Best of luck in finding the best VPN for your own, personal wants and needs!
Contributed by: Mark Soto , Cybersecurity Expert, Owner of Cybericus
As the owner of Cybericus - a cybersecurity firm in Milwaukee, Wisconsin, Mark Soto specializes in ransomware prevention...
Read Full Bio...Leave your honest feedback
By leaving your honest opinion you can help thousands of readers to choose the best VPN. We accept genuine & helpful user feedback, either positive or negative. Have in mind that biased feedback will not be published. If you want to share your opinion, experience or advice, we want you to spill the beans!